Last Updated on January 6, 2023

The coronavirus and its influence on the work environment need no introduction. A decade ago, you may have laughed at the prospect of working from home. Today, you’re charging your MacBook and putting on a pot of coffee in readiness for the day’s work — all from the comfort of your front room.
The numbers from Global Workplace Analytics tell us that over 4.3 million people in America work from home on a full-time basis. We always find ways to adapt to situations, regardless of how inconvenient they may be.
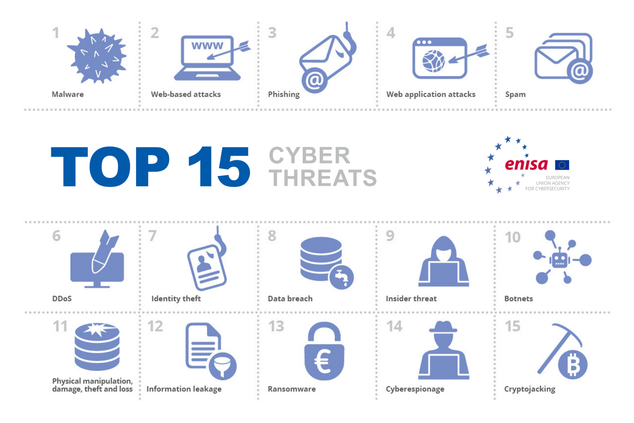
However, this adaptation has to be complete. For a remote team, mobile security is a focal point that needs addressing. More importantly, it extends to every remote worker regardless of how low tech their job description may be and whatever the remote tool they’re utilizing.
From the technicians who receive details about urgent repairs in the field via the internet to the Android engineers who do their work with high-tech systems, mobile security is important for everybody. Where a remote team is concerned, you can never be too careful.
Of course, mobile security is not a new concept. Most organizations are well aware of the potential dangers that come with working from home. However, COVID-19 and the upturn in remote work mean it’s important to design a security plan that accounts for all employees, remote or otherwise.
Social media giant Twitter announced in late 2020 that some of its employees will have the option to choose remote work permanently. In the same timeframe, Google and Apple rolled out their work-from-home plans.
This effort to cater to remote employees is not just for tech giants. Whether you have a team of 10 or 50, it’s important to put measures in place to protect data exchange and communication with remote employees.
Here, we will help you do just that. You can start with a secure virtual telephone system that keeps you in the loop with your remote workers. Keep reading to find out the most effective ways to ensure mobile security for a remote team.
Attitude to Authentication and Passwords
You’d be surprised at people’s laxity toward passwords. In fact, up to 65% of people reuse the same password across multiple platforms. And, when you think about it, your remote employees are bound to make the same mistakes.
As a result, it’s up to you to take a stand that impresses on your remote team the importance of passwords to mobile security. For starters, ensure your employees strengthen all of their logins.
This “cleanse” should not be limited to the online company workspace. The most effective cybersecurity tips dictate that this should extend to phones, wireless routers, home offices, and laptops. As long as it can be considered a network node, it needs a strong password.
The best passwords have a combination of numbers, letters, and symbols. It’s not enough to use strong passwords. As much as possible, your remote employees should use different passwords for different devices. Then, even if there is a breach, it can be easily contained.
Two-Factor Authentication
To ensure the mobile security of your remote team, consider employing two-factor authentication on all platforms. Also known as 2FA, this mobile device management feature requires employees to provide a special code even after inputting the correct password.
Typically, this one-time code is sent to a channel that can only be accessed by the remote worker. This may be via email or text.
Two-factor authentication adds an extra security layer that deters hackers and other nefarious characters. Even if they have the password, they’ll still need the 2FA code to gain access to your remote employee’s online accounts.
Use Encryption
While attackers may try to steal your remote worker’s password, others try a back door approach. It’s completely possible to lose sensitive data to a hacker via a home Wi-Fi system.
Therefore, in addition to a strong password, require your workers to use the latest encryption for their home routers. For instance, Wi-Fi protected access (WPA) encryption will do the trick. Similarly, you can go one step further by using advanced WPA3 encryption. To ensure the functionality of this encryption, it’s important to cancel the option of a guest password.
Finally, remind your remote workers not to share sensitive data over public Wi-Fi. With mobile security and cloud computing, the devil is in the details!
Do Data Backups At Regular Intervals
When we think of mobile security, we immediately assume it’s a third-party trying to steal proprietary data. However, data loss is an aspect of mobile security you should not ignore.
This data loss does not necessarily have to be caused by a hacker working behind the scenes. Uncontrolled data downloads can expose a network to malware that compromises important data.
For an enterprise, the corruption of important data can be a huge loss. To avoid this situation, encourage your employees to back up all company and personal data on a regular basis. An employee schedule template can help you keep track of data backups.
Employ Tracking Systems for Work Equipment
Digital tracking technology can be installed to provide real-time information on the condition and location of any equipment. This type of mobile security is not limited to devices with an internet connection.
It may increase your operating expenses, but location tracking technology can save the day. For instance, say you have a remote engineer who has to conduct tests with expensive analytical equipment. If this equipment gets lost in the field, it’s possible to track its location down to the nearest foot.
However, you need to have pre-installed the tracking technology, so take that pre-emptive step today!
Physical Security
Tracking technology is a form of mobile security that works after the fact. To really ensure the security of a remote team, you need measures to prevent thefts. It’s all a part of how the digital workspace is evolving. After all, you need these devices to access the digital workspace.
Just like bicycle locks keep a bicycle in the same place, it’s possible to do the same for employee equipment. For instance, tech giants Panasonic provides special mounts and docks that secure gadgets to vehicles and desks.
If you have a remote worker that’s constantly on the go, this is a great way to prevent theft. In addition to this, you should also impress vigilance on your employees.
As an illustration, there’s no circumstance where vital hardware should be left unattended. This brings us to the next point.
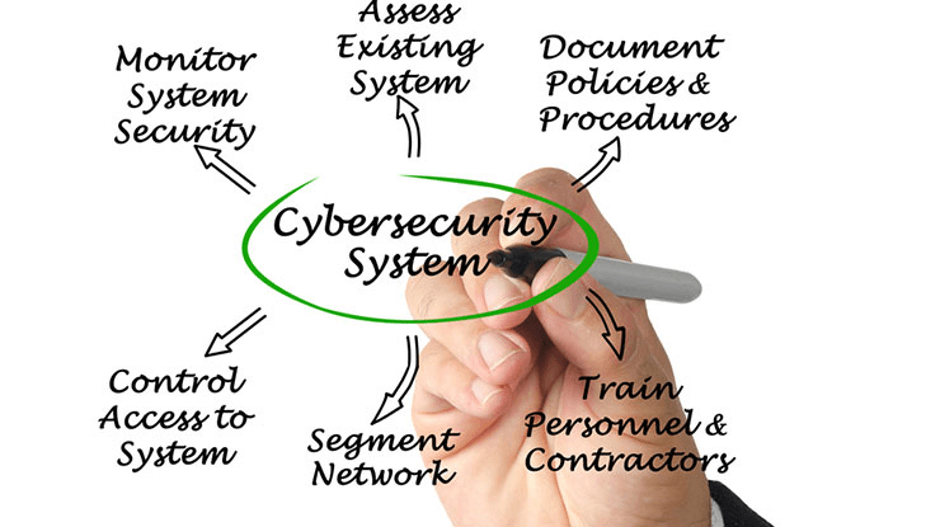
Train Your Employees
As many as 28% of mobile phone owners don’t use a password or screen lock feature on their phones. It may not be their primary workstation, but a sizable number of remote employees access their workspace with these unprotected phones.
Sure, they can use a small business phone line. But you also have to help your employees unlearn this attitude toward mobile security. You can do that via a detailed webinar session.
During this virtual session, enlighten your staff on the security measures they need to take. This should include information on avoiding public internet, installing apps from unverified sources, clicking on phishing emails, and using safe file sharing sites.
You may not be able to cover it all in one session. Or you may need to change the strategy depending on how your mobile security evolves. In instances like this, it’s best to schedule regular sessions where you can provide updates to mobile security and data protection trends.
100% Security Even with Remote Work
The flexibility and ease that come with remote work mean it’s here to stay. There are so many tech innovations making remote work easier. Take a vanity number lookup as an example. With it, you can make it simpler for remote workers to reach you.
But managers have to pay attention to the possibility of security issues and breaches that come with remote work. Websites like eSecurity Planet make it easier to stay on top of cybersecurity protocols.
We are also doing our part. Above, we have described relevant strategies to ensure the mobile security of your remote team. With these steps in place, you have one less thing to worry about in relation to work. Get started on them now!

Author Bio
Elea Andrea Almazora– RingCentral US
Elea is the SEO Content Optimization manager for RingCentral, the leader in global enterprise communication and collaboration solutions on the cloud. She has more than a decade’s worth of experience in on-page optimization, editorial production, and digital publishing. She spends her free time learning new things.