Last Updated on October 11, 2022

Whatever your industry, it is important to think about how your employees work for you. If you are dealing with sensitive business data, you want to make sure that your employees are not compromising your security. There are several different measures you can take, and an MDM policy codifies these best practices to avoid confusion.
Indeed, an MDM policy is a crucial measure since cybercrime was projected to cost businesses $6 trillion in 2021. But what does an effective MDM policy look like? This article outlines the concept and discusses some key considerations for your own MDM policy.
What is an MDM policy?

An MDM policy is a set of rules and guidelines on how employees use technology when they work for a business. It covers devices such as smartphones and laptops, as well as those that are not typically portable (e.g. desktop computers). It shares some things in common with ISO certification, which determines (among other things) who can access certain information within a business.
The main purpose of an MDM policy is security; it allows a business’ IT department to protect sensitive information from cybercriminals. This is important because while sensitive data can be stored on mobile devices, these devices can also grant access to further information (within a business’ internal networks, for instance). An MDM policy also offers guidelines on what devices can be used for, what can be installed on them, and other concerns.
A detailed MDM security policy can even help you to acquire leads. This is because by creating a broad set of gatekeeping standards, your employees can do their jobs safely from multiple locations. It also means any problems with devices are easier for your IT department to fix.
The end result of this is increased retail sales, which is naturally something any business benefits from. If you have not formalized (or updated) your MDM policy for a while, now is an excellent time to do so.
An MDM policy applies to everyone who uses devices during work for you. This includes both full-time and part-time staff, as well as temporary contractors.
Do all MDM policies look the same?
MDM policies tend to fall into one of four broad categories. Each of these includes more detailed rules about how the device is used in practice, and reflects the unique preferences of each business.
Bring Your Own Device (BYOD) means each employee is responsible for buying and maintaining their own device. Businesses may have limited control over this device, and rely on trusting employees to both use it properly and secure their devices against exterior threats. It works best if businesses and employees agree on certain measures, like separate user profiles and password protection.
Even if a business chooses to enforce an MDM security policy on these devices, BYOD has its drawbacks. Sensitive data is vulnerable if there is no secure Wi-Fi or firewalls to protect it (e.g. if the employee uses it off work premises). It also blurs the division between work time and down time, creating a stressful environment for employees.
Corporate-Owned, Personally Enabled (COPE) means each work-related device (and relevant additional products, such as data) is purchased by the business. While an employee can use it as a personal device, they are subject to certain restrictions on things like downloads and other activities. Separate user profiles are essential; indeed, the business benefits from broader control over the device itself.
The obvious drawback of this option is a significant upfront cost, depending on how many employees need devices. However, this cost is often offset by the financial and reputational costs of a security breach. COPE devices may make team task management more straightforward, and simpler to incorporate process management software.
Choose Your Own Device (CYOD) allows employees to pick from a list of approved devices (based on security and other considerations). The employee might purchase the device, which has an impact on business monitoring.
Corporate Owned, Business Only (COBO) applies to smartphones, and supplies employees with a phone exclusively for business purposes. This is a good way to protect business data. However, in practice it can be tedious for an employee to carry around a second phone. The phone is also vulnerable to other problems, like accidental loss or damage.

What responsibilities do businesses have?
A business needs to determine the shape of the MDM policy and define its fine details. While protecting itself is a key concern, this protection needs to respect the concerns and dignities of the employees subject to it.
You can use these best practices as a starting point for your own MDM policy, but remember that it is not a static document. You can amend or expand the policy in response to employee feedback or changing technologies if you feel it’s appropriate to do so.
Hardware and Software
A good starting point is to decide which devices your employees can use to access your network and business data. You will probably want to include laptops and smartphones, for example, but you might want to limit access to specific brands or operating systems. The more options you have, the bigger your IT workload becomes—and the more threats you have to worry about.

It is also worth making an explicit ban on devices that have been rooted or jailbroken. This is because these devices allow malware to be installed, and present a significant security risk. Devices that access the internet in unconventional ways (like smartwatches or games consoles) might fall under a business ban as well, for practicality reasons if nothing else.
Another consideration is what can be installed or accessed on a business device. Approved apps allow you to encrypt data and ensure employees can communicate effectively with one another (if you all use the same project management software, for example).
If you feel it is necessary, you can block certain apps and websites from being accessed at all on company devices. Conversely, your IT department may want to consider website whitelisting. This is a list of approved websites that employees can use without opening you up to security issues.
Security
As well as choosing appropriate hardware and software, businesses need to think about security in a broader sense. This idea applies on multiple levels within your workplace.
On a basic level, businesses need to restrict data access to those who need it. Make sure all accounts, devices and networks are protected with strong passwords and that these are regularly updated. Two-factor authentication is a simple but effective security measure, and is definitely worth considering for the login process.
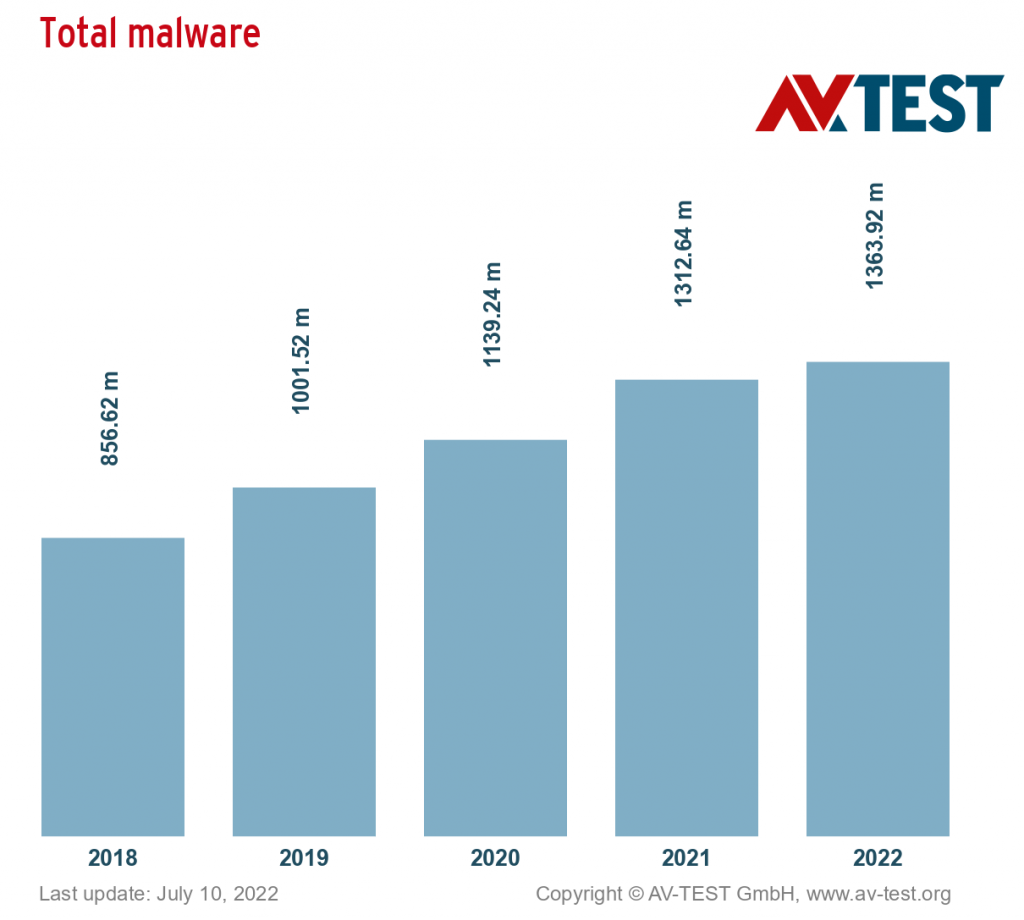
While blacklisting rooted devices helps you avoid malware, installing anti-malware software is still recommended. Spyware, ransomware, and trojans are all major threats, but all malware presents a risk. You should also make sure to download software and hardware updates quickly; in many cases, these fix vulnerabilities that have been recently discovered.
Make sure to educate your employees about your security measures. Show them how to use your approved hardware and software properly, the security procedures they need to follow, and what common threats look like. These measures work in tandem to minimise security threats.
But even with all these measures, it is worth seeing how your business fares against a cyber attack. Penetration testing subjects your digital assets to a simulated attack; in doing so, you allow your IT team to identify possible access points, vulnerable targets and anything left behind.
Seeing what your security measures are capable (or incapable) of doing helps them to be as strong as possible. It is worth folding this practice into a broader QA process, and keeping up to date with top QA blogs as well.
Documentation
Accurate record-keeping is another key task for businesses. Much of this is obvious—you need to have a record of your employees, the devices they use, their accounts/credentials and the networks they access. If you experience a cyber attack (real or simulated), you need to document what happened, including any vulnerabilities that you identified. RPA tools may be able to make this documentation easier.
If your business uses a BYOD policy, documentation becomes a much more complex issue. This is because there are significant privacy concerns about the data you extract from personal devices. Separate user profiles can make this task simpler, but it is vital you have a clear discussion with employees about what data you can (or should) extract from a device, as well as your MDM policy more broadly.

What responsibilities do employees have?
A business will have established much of what an employee can and cannot do in a professional capacity. However, it is important to think about employee responsibilities as a separate issue, especially since some concerns spring from their actions in or out of the workplace.
Ownership
If an employee uses a device supplied by the business (COPE), they need to treat it with proper respect. Usually this is an issue of upkeep; employees have to keep a device in good condition, and install software updates promptly. They should not tamper with any security software installed on the device, or make any other unapproved modifications. If the business’ MDM best practices include automatic app updates, these should not be interfered with either.
If an employee leaves the business, they must return the device (and any related items) to the business before departure. They must also return the device if the business requests this, regardless of employment status. Loss, theft or damage are typically things the employee must compensate the business for, barring exceptional circumstances. Loss and theft in particular must be reported promptly, to ensure bad actors do not access sensitive information.

If an employee uses their own device (BYOD), this obviously is not an issue. However, employees still have to ensure their device meets the technical standards (in terms of hardware and software) that the business requires.
Usage
Typically, employees should use business-supplied devices for work-related tasks only—if they want to use the device for personal reasons, they should get permission to do so. In any case, the employee mustn’t use data excessively.
Employees must also think carefully about the specifics of their device usage. Most of the time, this refers to the specific software and services they access. This is important, because the business-approved ones ensure greater protection from security breaches.
On a basic level, employees should use secure Wi-Fi, an approved web browser and a corporate VPN for general web activity. They should also avoid using personal email addresses to transfer business-related data.
Downloading unfamiliar files or using file-sharing sites that the business has not explicitly approved should be prohibited. Data should be regularly backed up, and if employees use external drives these ought to be encrypted. Moreover, while it sounds obvious, employees should not leave logged-in devices unattended in public places or other high-risk areas.
Privacy
A business will track at least some activity an employee undertakes on a device within the MDM policy, and this can include highly sensitive details like call logs and physical location. Employees need to make sure they understand what data is being collected (and for what purpose) but they must also be able to challenge this data collection if they feel it is unjustified.
Start your MDM policy on the right foot with AirDroid Business MDM Solution today!
In Brief
Mobile Device Management is about communicating best practices around device usage in a clear, respectful way, via business process maps or some other delivery method. While it is largely concerned with technical standards, a good MDM policy cannot overlook the human element. It has to account for the ways people actually use technology, their personal expectations of their business, and what life looks like outside the workplace.
Good businesses seek some input from the employees, particularly around privacy and data access. It is vital for employee trust and morale that everyone understands what is expected of them, and that they feel they have appropriate influence over the rules they are subject to. People must be able to voice concerns without fear of reprisal, whilst maintaining professional standards and respect for security concerns.
Author’s Bio: Alister Esam is the CEO and Founder of Process Bliss, a work management software that is reinventing how businesses execute day to day tasks. He is an expert in strategic planning, business process management, and business process optimization. With more than 15 years of experience in helping businesses run at peak efficiency, Alister has dedicated his career to make work easier, and more motivating for managers and employees alike. Here is his LinkedIn profile.