Last Updated on August 4, 2022

We are observing a global paradigm shift in what we call a “workspace” – thanks to the massive popularity of virtual working. The past year has shown us that remote work is not only practically feasible but holds the capacity to become the next workplace trend.
A Gartner study shows that 80% of surveyed companies are ready to offer remote work at least part-time in the post-pandemic world. At the same time, about 47% of companies plan on offering full-time remote work.
Companies have realized that the benefits of remote work go beyond maintaining employee safety. It costs less to operate, promotes work-life balance, and attracts rich talent.
About 38% of 699 CEOs surveyed by PwC want to make their business model increasingly “virtual by adding digital products and services.”
While virtualizing your office to welcome the next generation of remote workers is surely lucrative, it isn’t devoid of caveats. Virtual working comes with its own set of challenges that may end up nullifying the benefits, if not addressed properly. Especially, when it comes to laying the infrastructure for productive virtual work.
If you too are setting up a virtual office for your team, it’ll be only wise to apprehend the mobility challenges that await you. What steps you can take to ensure a smooth remote work experience, and how you can align business process needs in your virtual work arrangements.
1. Communication Challenges
Communication is the weakest thread in any virtual office, and yet the most significant one. Establishing strong and effective communication channels often becomes a challenge for offices that aren’t used to working virtually.
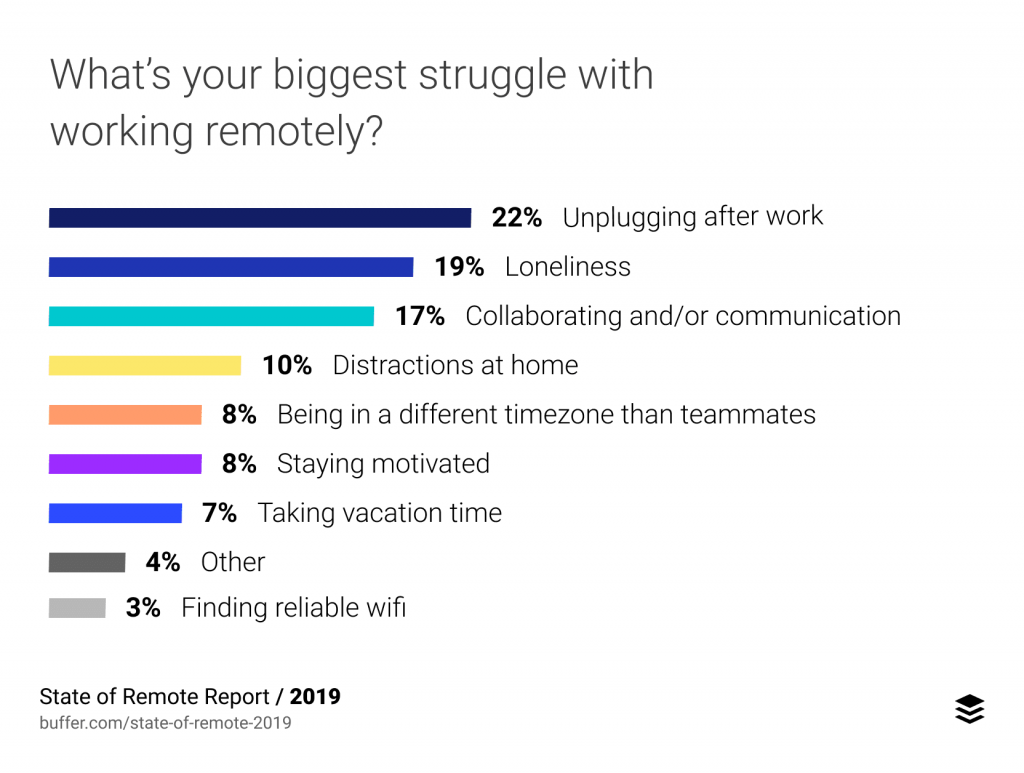
In a Statista survey, about 35% of respondents report “collaborating with colleagues/clients” to be a remote work challenge. Most of these challenges are associated with configuring the right set of tools and practices that facilitate unhindered communication.
Key Aspects of the Communication Challenge
- • Remote offices find it hard to work on projects that require multi-party collaboration such as graphic design, marketing, etc.
- • Remote workers feel disconnected from their teammates due to a lack of real-time communication.
- • Projects suffer due to ineffective communication on deliverables, deadlines, etc.
- • Project Information sharing (files, tasks, etc) becomes a hassle with team members being in different geographical locations.
How to solve Communication Challenges?
In an office, we have the luxury of walking up to our manager or fellow workers to quickly resolve doubts and catch up on their day. But when it comes to communicating virtually, each phone call seems extra. This is because virtual working is psychologically different.
To establish a free-flowing conversation that tries best to not be intrusive, you need to cater to three kinds of communication channels.
- • Real-time Communication: Zoom meetings, phone calls, instant messaging and everything that involves real-time information exchange falls in this category. The team needs a go-to real-time source of communication that makes everyone easily accessible. For virtual teams, video meeting software and VoIP calling tools are the best as they provide a seamless communication experience. The team members shouldn’t have to think before dialing a fellow colleague and an atmosphere of open communication should be established.
- • Asynchronous Communication: Emails, task comments, discussion boards – all refer to communication where parties exchange information asynchronously to each other. This kind of communication supplements real-time communication to enhance the collaborative experience. It is highly recommended to use a Team Communication Tool so that all kinds of announcements and @mentions can be propagated without having to get on a phone call each time.
- • Project Communication: At last, the team needs to be aware of the upcoming changes to the project, individual tasks, and HR sessions for the week. All of this requires a centralized portal where all project and workspace-related information is posted. Setting up a project communication tool for your team is a great way for dealing with the communication lag that remote workers may end up feeling.
2. Device Management Challenges
If you think that employee-owned laptops and phones are perfect for telecommuting and we’ll just put a VPN firewall on them, you may be mistaken. Your virtual office needs devices that you can remotely configure and control for maintaining harmony in your business processes.
Apparently, a large chunk of employees use their personal laptops for remote work, and many of them haven’t received the necessary cybersecurity training. This kind of negligence is akin to purposefully exposing your confidential business information to cyber theft.
Key Aspects of the Device Management Challenge
- • Companies asking employees to use their own devices may not have proper BYOD policies configured.
- • Employee-owned devices may not meet the compliance standards requisite for remote work.
- • Arranging portable devices for the entire workforce may get too costly for the company.
- • Employees may suffer configuration issues for critical business apps, which impacts productivity.
How to solve Device Management Challenges?

In a scenario where an increasing number of virtual offices rely on employee-owned devices, and the costs for procuring new work-from-home compliant devices may be too much, the best bet is to adopt an Enterprise Mobility Management solution.
These solutions enable your company’s IT staff to configure, monitor, and control devices from a central hub. You can install firewalls, monitor activity across all laptops, and trigger alerts in case a malicious activity is found. These solutions blend well with employee-owned devices, allowing them to function productively without drifting away from business compliance needs.
If your office has a stronger reliance on mobile devices, you can go for a Mobile Device Management solution that lets you enforce the same policies on mobile devices. With one click, you can change permissions across devices, bulk enroll smartphones to meet your company standards, and protect sensitive business data from being misused.
With growing threats to device safety, EMM and MDM solutions have become highly scalable. They’re no longer limited to big organizations because everyone is equally vulnerable when so many of us are working remotely. It makes sense to first protect the employee-owned devices as you kick-start your virtual office.
3. Data Security Challenges
You wouldn’t pray for this correlation to be true but in 66% of Indian firms, remote work is being linked to data breaches. These firms reported at least one cybersecurity incident since they shifted operations to remote working.
There are two primary reasons behind this; first, the organizations shifting to remote work haven’t adopted stringent data security policies, and secondly, cybercrime activity has surged in order to capitalize on the vulnerabilities that poor data protection brings with it.
Key Aspects of the Data Security Challenge
- • Organizations don’t have the necessary data security policies and implementations in place.
- • It is hard for IT staff to configure the same level of data security for remote devices, as they would in a controlled office environment.
- • It is easier for cybercriminals to steal data from vulnerable devices being used by remote employees
- • Organizations put an insufficient effort in training employees towards social engineering, phishing threats, etc.
How to solve Data Security Challenges?
Data security challenges can be best resolved by strengthening the following three core areas:
- • Introducing a strong data security policy and awareness: Creating a data security policy is the first step towards battling cyber threats. Measures like enforcing a 14-day password reset, using two-factor authentication, and whitelisting authorized IP addresses, should be paid attention to. The second step is to provide mandatory cybersecurity training to all employees working remotely so that no weak link is left behind.
- • Adopting Data Security Tools: Data Security tools that enable administrators to execute system hardening, employ remote access, and block unauthorized websites must be adopted. In many cases, you will be able to access these tools in your MDM solution.
- • Following a Well-planned Access and Authorization Framework: There needs to be a hierarchical framework for allowing access to sensitive business data. Levels of access and authorization should be configured for all kinds of critical resources. Remote work doesn’t mean, everyone has access to every resource just to make things convenient for remote workers.
4. User Management Challenges

This is one of the less talked about challenges because managing your remote workforce and their user accounts sounds easy in the beginning. You only realize the challenges when the team expands and there are just too many passwords to manage, alongside the long list of authorized devices.
About 59% of IT decision-makers have expressed favorability towards forming a strong Identity and Access Management (IAM) strategy, in order to cope with user management challenges. Poorly configured IAM can become an instrument for hackers to leverage upon.
Key Aspects of the User Management Challenge
- • User accounts need to be configured with the right IAM policies to prevent unauthorized access to critical resources.
- • In remote environments, managing user accounts across multiple business applications becomes a challenge
- • If SSO is not implemented with the right security measures, remote workers struggle to access the resources they need which impacts productivity
- • User management tasks such as password policies, user rights, and application security can get challenging for IT administrators
How to solve User Management Challenges?
Most User Management challenges become threatening when the IAM doesn’t abide by the right policies. In order to ensure that IAM is rightly configured, it makes sense to develop and implement an IAM strategy, which provides smooth access alongside fine-grained identity control.
For this, you can look for an Identity Management Solution that helps you quickly set up a strong identity policy for your organization. Some favorable market options are: MS Azure Active Directory, Lastpass for Business, Auth0.
Most of these solutions deeply integrate with your software applications, providing you a flexible way of managing identities. You can set up strong password policies, give or revoke access on the fly and enable SSO for increased security.
The good part is that a single solution lets you create a fully functional directory of users no matter if they work remotely, in-house, or on contract. But for the remote workforce, such a solution increases reliability and reduces identity risks.
5. Compliance Challenges
At your physical office, a number of workplace compliances are always in action such as OSHA’s General Duty Clause that ensures workplace safety. But as your office gets virtual, many of these compliances become challenging to maintain, with even more compliances entering the scene.
Compliances are important both from a security standpoint and from the legal purview. You wouldn’t want to invite any negative consequences from either side. The real challenge with the remote workforce is that you have limited control over the employee’s workspace, making compliance harder to enforce.
Key Aspects of the Compliance Management Challenge
- • Data Compliance – not following GDPR guidelines while recording and managing employee or customer data.
- • Security Compliance – If you’re a financial business, you’d want to ensure regulatory compliance such as PCI-DSS, to avoid cybersecurity risks.
- • Legal Compliance – Everything from classifying your remote workers as exempt or non-exempt, to offering the Affordable Care Act comes under legal compliance.
- • Mobility Compliance – Enterprise Mobility also demands a number of compliances to be met vis-a-vis how you manage employee data, and provide access to critical business resources.
How to solve Compliance Management Challenges?
Compliance Management challenges can be best met by first understanding the compliances that affect your operations and staying vigilant about your remote work policies. Drafting non-compliant policies can land you in trouble really easily. In most cases, you’d have to be wary about the solutions you’d be using in your virtual office.
The best way to stay compliant is to train the policymakers on meeting virtual office compliances. It involves everything from employee onboarding to enterprise mobility. Using tools that are compliant with workplace cybersecurity needs, and best practices can also come in handy.
This Wolters Kluwer article offers expert insights into compliance for remote employees that your organization should be aware of.
You might not have expected so many challenges would be waiting for you as you adapt to the virtual way of working. But that’s the thing! No one does, and it occurs to them mostly when a workplace incident sends out alarms ringing. By learning about these challenges, you can have your remote employees collaborate better, gel into your core teams, and while you scale operations without worries.

Author Bio:
Vartika Kashyap is the Chief Marketing Officer of ProofHub — a project management software loved by thousands of teams and businesses across the globe. A noteworthy personality in the global marketing community, Vartika writes to create awareness about new trends in marketing and business management. She has been a regular contributor to platforms like Business2community, DZone, and Business.com. An undeniable ideal figure, Vartika has also been one of the most influential LinkedIn Top Voices for 3 years in a row. Her inspiring stories have generated a considerable following on these platforms. When she is not keeping busy with managing a talented marketing team, she likes to draft spirited write-ups that focus on building a winning team and using the team’s talents to run a successful business.