Last Updated on March 15, 2023

Mobile Device Management (MDM) is an effective way to manage your mobile devices, when it comes to usage and security. MDM can do the following:
- Track important information about each device
- Remotely secure mobile devices, in the event that they’re lost or stolen, AND
- Track mobile devices both by user and geographical location
Rather than relying heavily on traditional desktop computers, corporate executives are taking advantage of the power of MDM software as they upload and save data in the cloud. However, as more companies move to cloud computing, they can no longer be without MDM.

Why MDM Is Important?
Companies and businesses (including nonprofits) are moving towards cloud computing, along with other software that requires a good amount of MDM. As a result, employees are incentivized to bring their [your] own devices (BYOD), and use them in their companies’ secure network.
By allowing BYOD in a work policy, it brings the following benefits to a company:
- Employees have more flexibility in their work.
- Employers see increased efficiency in their workforce’s work. AND,
- Employers enjoy lower equipment costs.
However, in the recent decade, MDM has become a priority for companies, since cybercrime is happening far too often these days. As a result, corporations are implementing MDM tactics more and more to reduce the likelihood of their businesses falling victim to cybercrime. With that in mind, this guide will give you a guided tour on how you can manage your devices like a corporate executive!
But first, let’s look at some terminology to keep in mind, as we learn about MDM.

MDM Terminology
Here are some terms to know when talking about MDM. As mentioned before, BYOD refers to employees bringing or connecting their own mobile devices to their company’s network to use on the job.
- Content access is a connection to a back-end repository where users can deliver content (i.e. documents, shared presentation slides, etc.) to their devices. Here, users can keep in mind download restrictions and audit log to see who can access and download files.
- Enterprise mobility management (EMM) is a collection of tools, technologies, processes, and policies that are used to manage and maintain mobile device usage within an organization. EMM can also serve as a point of security for mobile devices, meaning that management can set a time for mobile devices to connect to their network, as well as downtimes when necessary to prevent devices from hijacking too much connectivity.
- Application management refers to applying and monitoring individual applications on a device. With that said, there are two types of application management:
- Preconfigured applications include a secure personal information manager (PIM) for email, calendars, and contact management, along with a secure browser provided by the EMM provider or a third party.
- Application extensions apply policies to applications by using a software development kit (SDK), or by wrapping.
- Mobile content management grants users access to mobile content within EMM suites. This normally has 2 roles to play:
- Secure containers are client-side apps that lets users store content (i.e. from emails and attachments) securely on a mobile device. EMM enforces these policies with authentication, file sharing, and copy/paste restrictions.
- Content push is push-based document delivery that controls document versions, alerts users of new files, and flags content expiration dates.
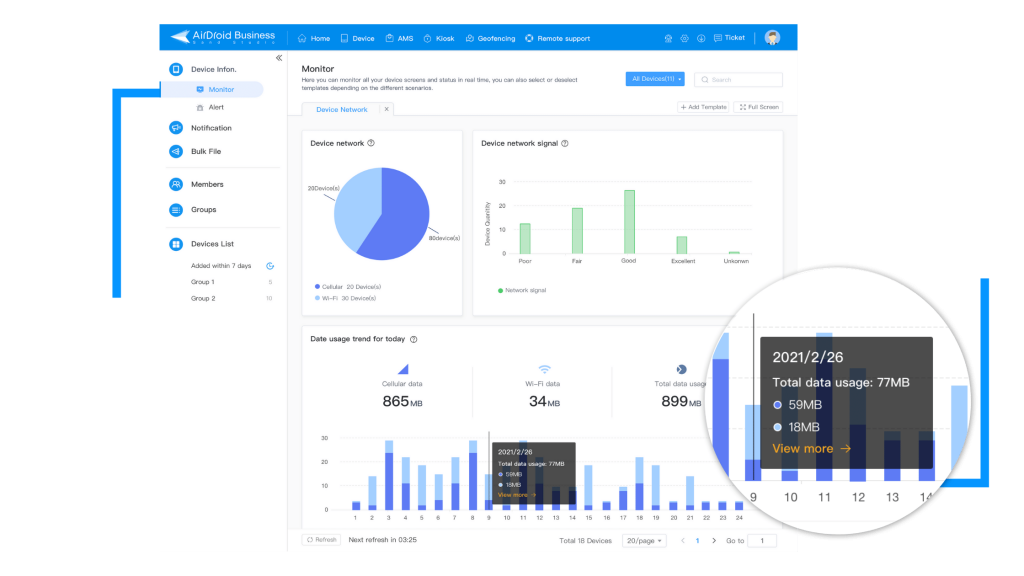
- Remote monitoring and management (RMM) – also known as remote IT management – is a type of software that is designed to help in managing IT service providers remotely, while proactively monitoring client endpoints, networks, and computers.
Approaches Taken So Far For MDM

There is no doubt that mobile devices have grown more apparent in today’s society. In fact, the usage of mobile devices has grown astronomically, that more and more companies are grown lenient, when it comes to their policies on such devices. There are even companies that ALLOW the use of mobile devices on the job, provided that employees still complete their daily tasks and follow company expectations.
With that said, businesses are doing everything that they can to regulate mobile device usage in the workplace. One of the ways that they do so is by seeing mobile devices as a collaborative and or communicative resource in day-to-day operations. However, this would have to be implemented safely, since there is that ever-present risk of cyberattacks, especially for mobile devices.
So, what are the best approaches so far in MDM?
The good news is, there are a few approaches to consider when implementing MDM solutions and policies. Such approaches include:
- The Corporate-Owned, Business Only (COBO) model is considered the first major MDM approach to have been implemented back in the mid-2000s. In this model, businesses would issue their employees “company” phones or computers, provided that employees use said devices ONLY for business purposes. Nowadays, this model has been rejected by most companies, because devices are now being used for more than just for work, but also for personal usage.
- The Corporate-Owned, Personally Enabled (COPE) model is where companies would issue their employees devices for not just work purposes, but also for personal use (with certain restrictions). The only notable restriction in this model would be that companies can still restrict certain apps that could potentially put company data at risk.
- Now, the Choose Your Own Device (CYOD) model allows employees to choose a preferred phone model, while the company still keeps the phone (remotely, in some cases), even while employees have them.
Nevertheless, companies have grown more lenient than ever, when it comes to employees using their own devices, just as long as comply with company policy to ensure data safety.
Streamlining Deployment With MDM
When MDM is implemented, multiple devices are streamlined in an organized plan that makes deployment easier in a company’s network. Now, companies must keep in mind that no device is from the same tribe; in fact, there are many operating systems to think about when streamlining device deployment with MDM:
- Windows
- Mac
- Chrome OS
- iOS
- Android, and so on
Knowing about what operating systems that employee devices run on can ensure an easier deployment of MDM solutions in the cloud. While this may take some manual configuration, MDM is still client-server-friendly, and can leverage the use of device notifications to comply with company policies.
How does MDM work?
Let’s say that you want to connect your smartphone to your company’s network. You would have to ask for permission from your supervisor(s) and the admins running the network to give your phone access.
Now, when connecting your phone to your company’s network, keep in mind that all mobile devices connected to the MDM server are categorized as “clients.”
From there, the MDM server will remotely push configurations, applications, and policies to a connected device, like your smartphone. Afterwards, IT admins will remotely manage all endpoints through the MDM server. In that case, your phone would be considered the endpoint that IT admins will have network connection to. Other endpoints might include laptops, Android tablets, iPads, etc.

Advantages Of MDM Solutions
With MDM solutions, companies are treated to many benefits, including:
- The ability to save time while automating repetitive tasks
- Increased productivity and efficiency from employees, especially when working from their mobile devices
- The ability to block non-essential applications (i.e. social media) from being used on personal mobile devices used during work hours
- Compliance regulations met (i.e. GDPR, HIPAA, and PCI-DSS)
- The ability to enforce strict data protection measures on all devices connected to the MDM server through a device lockdown mechanism
- The ability to manage devices remotely, AND
- The ability to have devices connected to the MDM server updated and patched without interrupting the user’s experience
What Makes A Good MDM Solution?
Now, an MDM solution has work perfectly, in order for a company to trust and use it. With that said, there are certain criteria that an MDM solution must meet when looking for one on the market. Such criteria include the following:
- The solution has to be cloud-based, so updates are seamless.
- It has to be fully managed, 24/7.
- Remote configuration and monitoring must be seamless, as well.
- It must reinforce the use of passwords, blacklists, and other security policies like data wiping (to prevent unauthorized access).
- It must incorporate geofencing to restrict access to specific data and applications at certain locations that a company may see unfit.
- It must backup and restore functionality of corporate data.
- It must log and report for compliance purposes.
- It must be able to accommodate to sophisticated devices.
- It must scale new users at a moment’s notice.
- It must send device alerts to admins regarding users’ attempts to bypass device restrictions.
Downsides of MDM
Despite their implementations, MDM solutions will only work if executed properly. That means companies should evaluate an MDM platform carefully to see if a solution will fit specific policies before making any commitment.
So, it is best to look at the possible downsides to having an MDM solution:
What happens if an employee resigns or is terminated? What will happen to their device under a company policy that allows employees to bring their own devices? Can saved or cached data be wiped off that device, or will that data stay on there? This is where executives must figure out how to handle devices whenever an employee resigns or is terminated.
Plus, the architecture can be a challenge in of itself. Why? Since the rise in popularity with cloud services and infrastructure, many organizations still prefer to have systems running in their own data centers. That’s why it’s important for businesses to figure out which MDM solution would be right for them (i.e. on-site, cloud, or hybrid options for MDM).
In addition, business operating direction is often changing, depending on the industry. MDM solutions also need to be adaptable to anything at a moment’s notice. That means that solutions should be able to easily updated, revised, and enhanced to fit business needs. As for companies, when choosing an MDM solution, they must understand not only what is provided to them today, but where development is headed next, so that the solution of their choice will best fit current and future needs. The flexibility to scale is also one important factor businesses should evaluate as well.
Finally, system integration is another factor to consider. The MDM solution of a company’s choosing must be able to integrate with existing security and management controls, along with workflows. That means ensuring that the right investments are made, so that integration is seamless. With the right MDM solution, it will enhance both security and efficiency, thus allowing admins to look after systems from a single access point.
How Executives Handle MDM?
Now that you have learned so much about MDM so far, how can you manage your devices like an executive?
It is fairly easy, actually. Here are some guidelines to follow when using an MDM solution for your devices at your company:
- Allow your employees (or team members) to choose devices that best fit their needs, while providing plenty of productivity, collaboration, and mobility on their end.
- Ensure that sensitive company information on mobile devices, or in the cloud, are made secure to prevent loss and theft, and maintain employee privacy. Features such as limiting device access to particular users is one way to avoid device tampering and data loss.
- Know the balance between costs and security. You should not have to sacrifice one for the other. But then again, security should always be your #1 priority.
- The IT department in your company should be responsible for managing and monitoring devices, securing data, and keeping work-related apps up-to-date in order to prevent any security issues:

Final Thoughts
Ultimately, employee-owned mobile devices are the norm, when it comes to remote workforce. Therefore, businesses must develop a plan to implement and manage mobile devices with an effective MDM solution. The last thing you want, as an executive, is to risk having your company’s network hacked and sensitive data stolen, due to an ineffective strategy.
With MDM, all devices – including personal – can be protected in the server, especially when being connected to the cloud. While it’s understandable that many businesses have their own unique needs, MDM solutions are customizable, and can be implemented at any time.
Undoubtedly, MDM is essential for every business imaginable. With cyber security threats growing more evident these days, it is important to make MDM work for you and your company.
Author’s Bio: Regina Wheeler is a writer and editor at Write My Research Paper. As an eLearning consultant, she tutors college-level students on a variety of subjects, including computer technology and coding.
[…] being said, organizations need to develop a clear and detailed policy about what devices employees can use, which devices can access certain networks, and which […]
[…] solution typically combines all aspects of management, including mobile device management (MDM) and mobile application development (MAM), along with other added capabilities to secure and manage email and other content. EMM […]